Solvo ReInvents Cloud Identity and Access Management with IAMagnifier
Security innovator launches an automated, visual and centralized cloud DevSec platform, reducing permission misconfiguration breach threats
Solvo, a security automation enabler for cloud development and production environments”, announced the availability of its “IAMagnifier” – a cloud SaaS security platform, enabling developers, DevOps and cybersecurity stakeholders working in cloud development environments to reduce potential cybersecurity threats caused by misconfigured access permissions to cloud assets.
To truly enable a secured, yet productive development environment, a “least-privileged” permission mechanism should be employed – by using this methodology, the access level for each asset is defined by answering the question “How can I prevent access to that asset from anyone or anything other than anyone or anything that is supposed to access it to perform their intended task?”
Recommended AI News: Treatment’s Global Library of Medicine Expands in Belgium
Today, security-minded developers and security stakeholders within the organization had to manually inspect security permissions configurations for each asset, compare the permission levels found within the specific asset’s configuration to the permission level stated by the relevant organizational policies, and if the actual permission level is too lenient – rectify the situation by updating the asset’s permission configuration.

In addition to the need to perform these set of activities for each individual asset, a task which might entail an enormous waste of time and effort, the permission level to which the “wrong” configuration should be updated to may not be the best one according to the specific characteristics of each individual asset.
“Solvo’s IAMagnifier turns this cumbersome, lengthy, inefficient, and error-prone process of managing cloud assets’ access permissions, into an automated, centralized, fast and decision-assisted experience,” explains Solvo’s Co-founder and CEO, Shira Shamban. “It does so by constantly inspecting the assets’ access permissions configurations, analyzing gaps between the current and desired permission level, suggests the needed changes to the configuration, and performs these changes if approved by the user.”
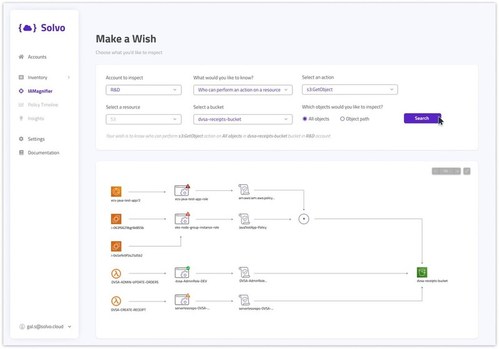
To present the most relevant and updated data about permission levels and potential risks derived from permission level gaps, Solvo’s IAMagnifier offers visual experience, which turns boring tables and records into easy to comprehend mapping of connections and dependencies between Roles, Policies, assets and users. The IAMagnifier also highlights what its analyzer has declared as “excessive permissions”, and suggests an alternative, least-privileged permission policy, which can then be enforced by the user just by approving the suggestion.
Recommended AI News: Rekor One To Be Deployed In Stamford, Watertown And Middlebury, Connecticut
Unlike traditional infrastructure default definitions or human-set definitions, the “excessive” permission status definition and the alternative permission suggestion the IAMagnifier highlights and suggests are derived from analyzing actual real behaviour of the application and finding the balance between preventing unrequired access by irrelevant stakeholders, and keeping an uninterrupted workflow for relevant stakeholders (i.e least-privileged).
Sylvie Veilluex, Solvo’s advisor and former CIO of Dropbox, added: “The team has been offering early access to the IAM Magnifier to selected customers, and the feedback has been nothing short of amazing. One of the CEO whose company was using the IAMagnifier went on to declare the ability to easily see the company’s security posture, and effortlessly enhance it, made scaling the company’s cloud and business infrastructure frictionless and even enjoyable.”
Solvo’s team will present IAM Magnifier during AWS’ Re:Invent conference, which takes place in Las Vegas, NV, between November 29th and December 3rd, 2021. Solvo will also be providing a free AWS S3 Bucket policy auditing during the conference, and visitors can schedule a meeting with the team for a chance to get back from Vegas with a win.
Recommended AI News: Amazon Web Services and Secure Code Warrior Join Forces to Enhance Developer-Led Security
[To share your insights with us, please write to sghosh@martechseries.com]

Comments are closed.