Users of Steam, Roblox, and Amazon Targeted; Popular Scams Stole 50M Passwords in 7 months
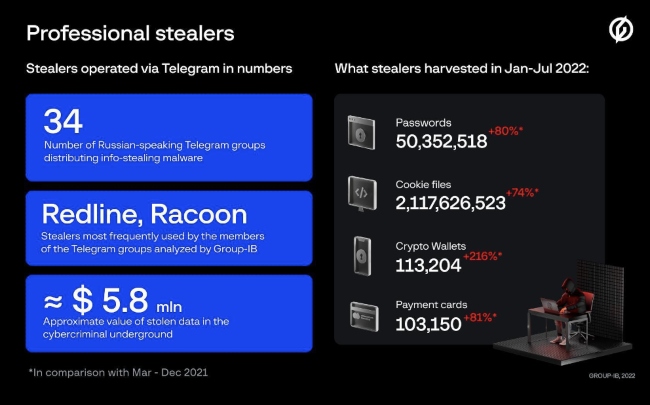
Professional scammers led popular scam schemes like Classiscam and others into stealing 50 million passwords in 7 months in 2022. These scams targeted users of Steam, Roblox and Amazon even as stolen logs and financial details worth USD 5.8 million were left exposed in the hands of professional stealers. Singapore-based Group-IB, one of the global leaders in cybersecurity, has identified 34 Russian-speaking groups that are distributing info-stealing malware under the stealer-as-a-service model.
This is what Group-IB found about the Roblox users and others who were targeted via cyber threats.
- The cybercriminals use mainly Racoon and Redlinestealers to obtain passwords for gaming accounts on Steam and Roblox, credentials for Amazon and PayPal, as well as users’ payment records and crypto wallet credentials.
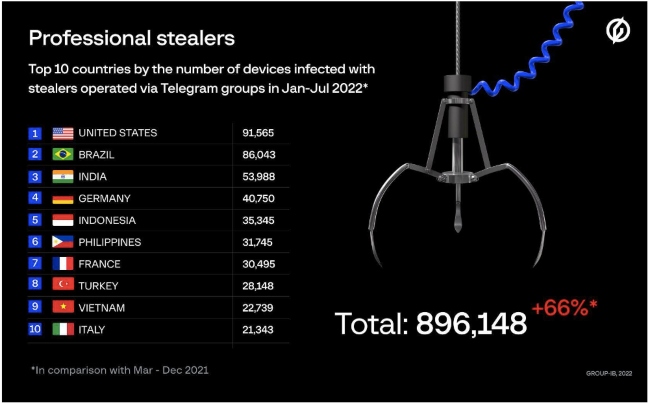
- In the first seven months of 2022, the gangs collectively infected over 890,000 user devices and stole over 50 mln passwords. All the identified groups orchestrate their attacks through Russian-language Telegram groups, although they mainly target users in the United States, Brazil, India, Germany, and Indonesia.
- In 2022, info-stealing malware has grown into one of the most serious digital threats.
Understanding Classiscam and how it works with Classiscam graduates in Roblox
By tracking the evolution of the popular scam scheme Classiscam, Group-IB Digital Risk Protection analysts revealed how some “workers” (low-rank online scammers) started shifting to a more dangerous criminal scheme that involves distributing info stealers. Moreover, the illicit business of stealers, which is coordinated via Telegram groups, uses exactly the same operational model as Classiscam.
Read More: EMURGO Ventures Announces Investments to Bolster EMURGO’s Growing Web3 Portfolio
An info stealer is a type of malware that collects credentials stored in browsers (including gaming accounts, email services, and social media), bank card details, and crypto wallet information from infected computers, and then sends all this data to the malware operator. After a successful attack, the scammers either obtain money themselves using the stolen data, or they sell the stolen information in the cybercriminal underground. According to Group-IB, stealers are one of the top threats to watch in the coming year. The threat actor responsible for the most recent attack on Uber purchased the credentials compromised with the Racoon stealer.
According to the Group-IB Digital Risk Protection team, (part of the Unified Risk Platform), the mass Telegram groups and bots designed to distribute info stealers first appeared in early 2021. By investigating a number of accounts, Group-IB analysts were able to confirm that members of several scam groups that previously participated in the Classiscam scheme began using stealers. In 2021 and 2022, Group-IB experts identified 34 active groups on Telegram. On average, such info stealer distribution groups have around 200 active members.
The most popular stealer among the groups examined by Group-IB is RedLine, which is used by 23 out of 34 gangs. Racoon ranks second: 8 groups employ this tool. Custom stealers are used in 3 communities. Administrators usually give workers both RedLine and Racoon in exchange for a share of the stolen data or money. However, the malware in question is offered for rent on the dark web for $150-200 per month. Some groups use 3 stealers at the same time, while others have only one stealer in their arsenal.
Having switched from scamming users of classified websites to stealers, some threat actors reproduced not only the hierarchy and model of Classiscam, but also its technical capabilities. In particular, Telegram bots that generate malicious content, communication between members, and all their shady accounting. The tasks of workers, the scammers of the lower-ranks, have also changed — they must now drive traffic to bait scam websites impersonating well-known companies and convince victims to download malicious files. Cybercriminals embed links for downloading stealers into video reviews of popular games on YouTube, into mining software or NFT files on specialized forums and direct communication with NFT artists, and into lucky draws and lotteries on social media.
Telegram Stealers world tour
Group-IB estimates that between March 1 (when Group-IB started researching the scheme) and December 31, 2021 stealers operated via Telegram groups were able to compromise 538,000 devices. In the first 7 months of 2022, Telegram stealers were found to be almost twice more active infecting more than 890,000 devices in 111 countries.
The top 5 most often attacked countries in 2022 were the United States, Brazil, India, Germany, and Indonesia with 91,565, 86,043, 53,988, 40,750, and 35,345 infected devices respectively.
List of countries in Asia Pacific by the number of infected devices include India, Indonesia, Philippines, Vietnam and Singapore. In India for example, from March – December 2021, the operators of the stealers in question infected 19,249 devices. In the first seven months of 2022, the number grew to 53,988. Scammers were able to retrieve 4,547,020 passwords, 4,657 sets of payment records, and 4,428 sets of crypto wallet information such as credentials, seed phrases, etc.
Indonesia closely follows with a total of 35,345 infected devices and where scammers were able to retrieve 2,372,893 passwords. The Philippines recorded a total of 31, 745 infected devices and Vietnam with a total of 22,739 devices infected and scammers retrieving 2,032,278 passwords. Australia had 5,794 devices infected and 549,640 passwords retrieved by scammers. Singapore saw 2,179 devices infected, with 185,689 passwords retrieved.
According to the analysis of Telegram groups, for the last 10 months of 2021 cybercriminals collected 27,875,879 sets of passwords, 1,215,532,572 cookie files, 56,779 sets of payment records, and data from 35,791 crypto wallets. In the first 7 months of 2022, threat actors stole 50,352,518 passwords, 2,117,626,523 cookie files, details of 103,150 bank cards, and data from 113,204 crypto wallets. The underground market value of just the stolen logs and compromised card details is around $5.8 million, Group-IB experts estimate.
According to Group-IB, in 2021, threat actors worldwide most frequently collected PayPal account credentials (more than 25%) and Amazon credentials (more than 18%). In 2022, the most targeted services are the same, namely PayPal (more than 16%) and Amazon (more than 13%). However, over the course of the year, cases of stealing passwords for gaming services (Steam, EpicGames, Roblox) in the logs have increased almost five-fold.
“The influx of a huge number of workers into the popular scam Classiscam — which Group-IB’s Unified Risk Platformidentified, at its peak, comprised over a thousand criminal groups and hundreds of thousands of fake websites — has led to criminals competing for resources and looking for new ways to make profits,” says Ilia Rozhnov, head of Group-IB’s Digital Risk Protection in the Asia Pacific. “The popularity of schemes involving stealers can be explained by the low entry barrier. Beginners do not need to have advanced technical knowledge as the process is fully automated and the worker’s only task is to create a file with a stealer in the Telegram bot and drive traffic to it. For victims whose computers become infected with a stealer, however, the consequences can be disastrous.”
Recommended: Daily AI Roundup: Biggest Machine Learning, Robotic And Automation Updates 29th November 2022
How to reduce Digital Threats in Roblox Environment
To minimize potential risks, Group-IB Digital Risk Protection experts recommend that users refrain from downloading software from suspicious sources, use isolated virtual machines or alternative operating systems for installation, avoid saving passwords in browsers, and regularly clear browser cookies. To prevent digital risks and unwanted consequences, companies should take a proactive approach to their brand’s digital security and use modern technologies for monitoring and response, such as Group-IB’s Digital Risk Protection.
Group-IB, with its headquarters in Singapore, is one of the leading solutions providers dedicated to detecting and preventing cyberattacks, identifying online fraud, investigating high-tech crimes, and protecting intellectual property. The company’s Threat Intelligence and Research Centers are located in the Middle East (Dubai), Asia-Pacific (Singapore), and Europe (Amsterdam).

Comments are closed.